Modern businesses operate in a complex, fast-moving digital world where cyber threats are increasingly sophisticated, and the risks to company assets and client data have never been greater. Without a comprehensive approach to compliance and security, organizations can expose themselves to costly incidents and reputational damage. Adopting a robust security program, supported by actionable best practices, is critical for maintaining customer trust, safeguarding sensitive data, and achieving long-term success. Organizations seeking specialized support should consider Expert NERC Compliance and Risk Management to strengthen their risk posture and meet regulatory demands.
Increasing regulatory scrutiny means compliance is not merely a checkbox but a continuous journey. The right combination of security measures supports resilience, helps prevent breaches, and demonstrates a proactive commitment to both customers and partners. Additionally, fostering a culture of awareness and vigilance across the workforce further enhances the ability to recognize and respond to threats early.
In recent years, businesses have faced an evolving array of threats, including ransomware, phishing, data leaks, and insider attacks. As regulations such as the GDPR and industry-specific frameworks strengthen, establishing and maintaining compliance has become central to risk management. Building a layered security approach ensures that organizations are not just reacting to risks but actively defending against them.
Effective cybersecurity is not just about technology; it also involves processes and people. Businesses that continually assess their vulnerabilities, educate employees, and incorporate robust controls are far better equipped to adapt as the security landscape shifts. By integrating these best practices, organizations position themselves for resilience and growth.
Zero Trust Architecture
The Zero Trust Architecture has become a foundational security model for organizations embracing digital transformation. Zero Trust operates on the principle of “never trust, always verify,” meaning every device, user, and request is authenticated and authorized before it can access company resources. Rather than assuming those inside the network perimeter are automatically trusted, controls apply equally regardless of a user’s location. This approach drastically limits attackers’ lateral movement, helping protect both on-premises and cloud-based systems. According to Forbes Technology Council, implementing Zero Trust can reduce the risk of both insider threats and external breaches.
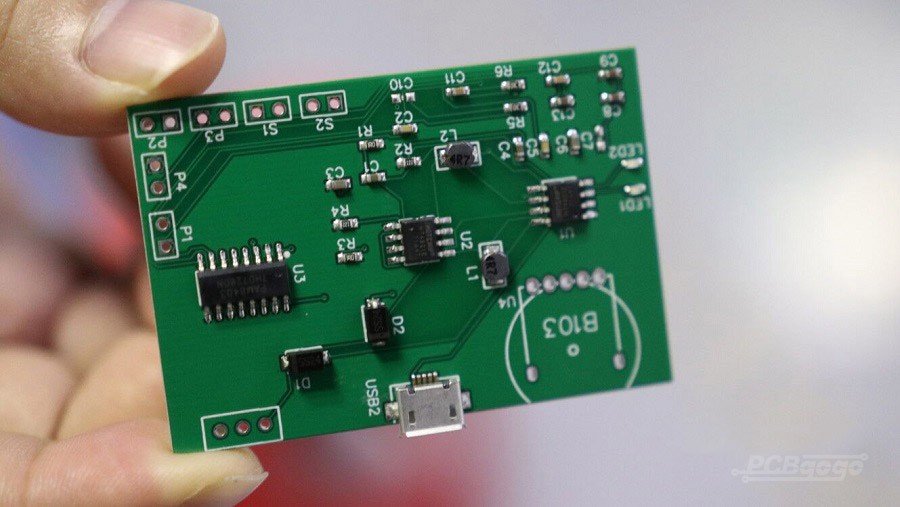
Regular Vulnerability Assessments
Staying ahead of potential attackers requires constant vigilance. Regular vulnerability assessments help identify exploitable weaknesses across hardware, software, and network configurations. By conducting comprehensive scans and promptly addressing discovered vulnerabilities, organizations avoid giving attackers easy entry points. Automated tools, when combined with manual testing, can provide comprehensive coverage. In regulated industries, scheduled assessments are often a compliance requirement, making them crucial for maintaining both security and regulatory standings.
Employee Training and Awareness
Human error remains a leading factor in breaches. Ongoing training and awareness programs equip employees to recognize and respond to threats such as phishing, social engineering, and password misuse. By embedding security into the organizational culture, businesses create a strong first line of defense. Innovative training techniques, like gamified learning and simulated attacks, can significantly enhance employee engagement and information retention, reducing the likelihood of mistakes that put the business at risk.
Multi-Factor Authentication
Multi-Factor Authentication (MFA) significantly strengthens account security. With MFA, users must provide two or more forms of verification, such as a password plus a fingerprint or a one-time passcode. This additional step thwarts most credential-based attacks, since compromising just one factor is not enough to breach an account. Implementing MFA for all critical systems and remote access points is considered best practice by cybersecurity leaders and required by many regulatory frameworks.
Data Encryption
Encrypting sensitive information ensures data confidentiality even if it is intercepted during transfer or exfiltrated from storage. Both data “at rest” (stored on drives or servers) and “in transit” (moving across networks) should use strong cryptographic algorithms and robust key management practices. Encryption not only protects privacy but also helps meet compliance requirements established by laws such as GDPR and HIPAA, as well as sector-specific standards.
Incident Response Plan
No defense is perfect, which is why a swift and coordinated response to incidents is essential. A well-documented, regularly updated incident response plan outlines roles, reporting channels, and step-by-step procedures for containing, investigating, and recovering from incidents. Tabletop exercises and simulated attack drills test the team’s response readiness, helping ensure that when an event occurs, the business can minimize damage and resume operations quickly.
Compliance with Regulations
Regulatory compliance is a cornerstone of responsible business conduct. Frameworks such as the General Data Protection Regulation (GDPR), the Cyber Security and Resilience Act, and industry-specific mandates set clear expectations for how organizations must manage risk, secure data, and report breaches. Staying current with changing regulations is vital, as non-compliance can lead to hefty fines and lasting reputational harm. Leveraging guidance from reputable organizations and legal resources can help keep businesses compliant as legal landscapes evolve.
Continuous Monitoring
Modern security is not a set-and-forget undertaking. Sophisticated monitoring solutions, such as Security Information and Event Management (SIEM) and extended detection and response (XDR) platforms, offer continuous surveillance against emerging threats. These systems aggregate logs from across the environment, flag anomalies, and automate incident triage. Continuous monitoring not only enables faster response but also provides evidence for auditors and regulators during compliance checks.
By diligently implementing these best practices, organizations can develop a resilient security framework that is prepared to handle both known and emerging challenges. Prioritizing compliance and security initiatives not only protects corporate assets but also inspires greater trust and confidence among customers, regulators, and business partners.